When many people picture cybercrime, they imagine hackers breaking into giant corporations with sophisticated tools and complex code. But for most small businesses, cybercrime today looks much more ordinary - and much more personal.
-
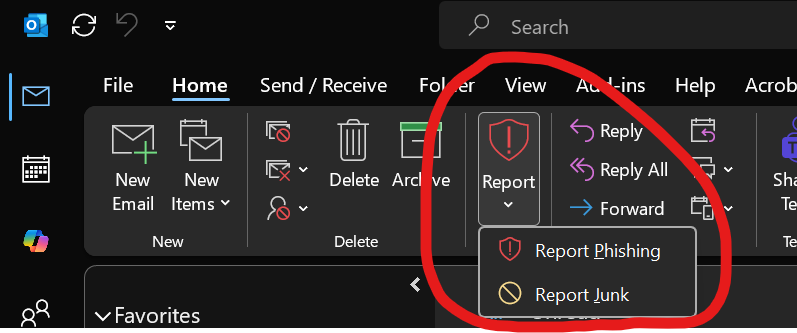
It looks like an email from a trusted vendor asking for updated payment information.
-
It looks like a voicemail that sounds like a company executive requesting an urgent wire transfer.
-
It looks like a Microsoft 365 login page that appears completely legitimate.
And increasingly, thanks to artificial intelligence, these scams are becoming harder and harder to spot.
The FBI recently released its latest Internet Crime Complaint Center (IC3) report, highlighting billions of dollars in losses tied to cybercrime, including growing losses from AI-assisted scams and cryptocurrency fraud. While the numbers themselves are staggering, the bigger takeaway for local businesses is this:
Cybercriminals are getting better at pretending to be someone you trust.
Read More.png)