Is love in the air…or is it a romance scam? Whatever situation you find yourself in, if 2026 is the year for you to find love this Valentines Day, it’s generally good practice to know the person you are talking to. What I mean by that is ensuring the person of interest you met through a website or dating app is a legitimate person that’s actions and words add up. Romance scams are currently one of the highest scam methods in America. When using social media or the internet in general, it’s essential to have security and knowledge equipped to protect yourself, your time, your heart, and your personal information. At Ekaru, we provide users with educational cybersecurity awareness training, not to frighten you but to inform you to make thoughtful decisions. To react proactively when situations arise, the best form of defense is not always security tools, its knowledge.
Read MoreTechnology Advisor Blog
Romance Scams - Protect Your Heart & Personal Information
Posted by Sarah Carroll on 2/10/26 4:49 PM
Tags: Internet, cybersecurity, Security Awareness, Cybersecurity, Smishing, Cybersecurity, Social Media, Cybersecurity Awareness Training, Romance Scam
In January, multiple updates for Windows 11 affected millions of users. These mostly consisted of security patches, bug fixes, AI implementation and a new feature in the mix to improve the user experience for Microsoft users. As we enter a new month, Microsoft has another wave of updates for users that can help improve their security posture, enhance some features and discontinued others.
Read MoreTags: Microsoft Windows Update, Wi-Fi, cybersecurity, AI, Windows11
Jan 2026: ATM Skimmers, Social Media Phishing & Windows 11 Recap
Posted by Sarah Carroll on 1/29/26 3:41 PM
Just because it is January, does not mean hackers are ceasing their cyber attacks on businesses and unsuspecting victims. This month, we have noticed scams such as stealing debit card information at local stores hitting close to home, sophisticated phishing attempts across social media accounts, particularly Instagram, and Windows 11 updates we’ve observed for users. At Ekaru, our goals are to provide users with the most up-to-date news for cybersecurity locally and across the US, while also providing tips to keeping you and businesses safe.
Read MoreTags: password, cybersecurity, Cybersecurity, Social Media, Windows11, ATMScam
Shutdown vs. Restart: What’s the Difference and Why It Matters for Your Business
Posted by Sarah Carroll on 1/23/26 12:38 PM
Have you been in the middle of a significant deadline with complete focus, then all a sudden your desktop shuts down abruptly causing your focus and productivity to cease? It happens to the best of us.
Read MoreTags: Slow Computer, computer security, cybersecurity, Computer Tip, Computer Shutdown, Computer Restart
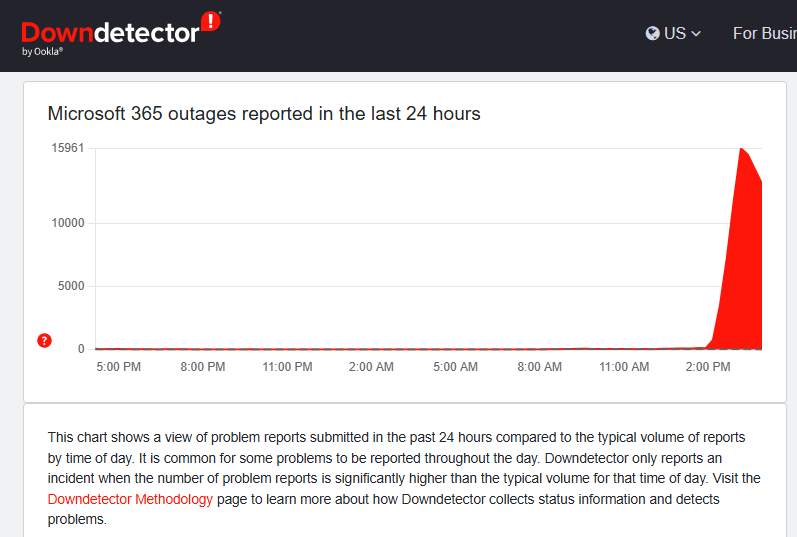
Microsoft 365 Outage Today: What's going on and why it matters
Posted by Ann Westerheim on 1/22/26 4:24 PM
Tags: Microsoft, Internet Outage, Microsoft 365
Why Rebooting Your Computer Is One of the Easiest Security Wins
Posted by Ann Westerheim on 1/21/26 5:42 PM
Security updates aren’t the most exciting topic—but they are one of the most important parts of keeping your business protected.
Right now, we’re seeing something that surprises a lot of people: about 13% of the systems in our community need a reboot. That means critical security updates are downloaded… but not fully protecting those computers yet.
Why reboots matter more than most people realize
Each month, Microsoft releases security fixes (often called “Patch Tuesday”). Behind the scenes, we carefully test critical patches within 24 hours, then roll out additional updates over the following week. This testing and deployment process is a core part of a healthy security program.
Here’s the catch: many of those security patches don’t actually take effect until you reboot. And we're seeing too many computers in our community that haven't been rebooted in too long.
Even more important, some patches are sequential. If the first update doesn’t fully install because the
Read MoreTags: Microsoft Security Patches, Patch Policy, cybersecurity
Before You Prove You’re Human, Make Sure You’re Not Helping Hackers
Posted by Ann Westerheim on 1/16/26 4:18 PM
Most of us barely notice CAPTCHA checks anymore.
You know the ones - the little box that says “I am not a robot”, or the quick image puzzle before you can move on. The little puzzle may ask you to select the images that contain traffic lights, bicycles, or crosswalks. We see them so often that clicking through has become second nature. In fact, many people associate CAPTCHAs with extra security, not risk.
Read MoreTags: cybersecurity, Cybersecurity Awareness Training
But wait - there's more! While we had a blog discussing Windows shortcuts to boost your productivity throughout the week, we also want to inform you of what’s to come for January 2026 updates regarding Windows 11. To provide an understanding of what’s coming your way, what you can expect for patch security updates, AI powered Copilot, PC features to devices, and more. Our intentions here at Ekaru are to provide our clients, and those searching for their next MSP, with the most up-to-date knowledge on all things cybersecurity and windows applications to ensure you are proactive and aware in the world of cybersecurity.
Read MoreTags: Security, Microsoft, Monitoring, cybersecurity, Windows11
Proceed with Caution: Post Holiday Surge in Phishing Campaigns
Posted by Sarah Carroll on 1/7/26 3:09 PM
Though it may be the beginning of a new year, the holiday remnants are evident when it comes to relentless cybercriminal activity. During the holidays, you had to be extra vigilant in managing your finances, buying gifts for friends/family, monitoring any unauthorized transactions, maintaining subscriptions, ensuring purchases came from legitimate websites and gift cards that were not tampered with. It’s understandable to feel fatigued in attempts to avoid being a potential target for cyber criminals. As hackers become more proficient with using AI tools and understanding your fears to enhance their phishing campaigns, the Ekaru team is here to help spread awareness of their evolving tactics, to prevent you from becoming their next victim.
Read MoreTags: Cybersecurity, email scams, cybersecurity, Text Scams, Fraud, Cybersecurity, Smishing, Identity Theft
As we move into 2026, we can reflect on the past year. 2025 has marked a significant shift with the integration of artificial intelligence into our workflows and daily lives. Whether welcomed or not, AI is now almost permanent part of the digital landscape, making it essential for organizations and individuals alike to stay informed and prepared, as cybercriminals seek to exploit these technologies for malicious intent.
Read MoreTags: cybersecurity, cybersecurity training, Artificial Intelligence, AI
.png)