We hear this all the time:
“We already have email security in place - we’re good.”
“We’re on Microsoft 365 (or Google Workspace) - they take care of that.”
And it’s easy to see why at first that feels like enough.
Platforms like Microsoft and Google provide a powerful foundation - offering the infrastructure, built-in protections, and security features that businesses rely on every day.
But here’s the part that often gets misunderstood:
They provide powerful tools - but they don’t replace a complete security strategy.
And even with strong protections in place…
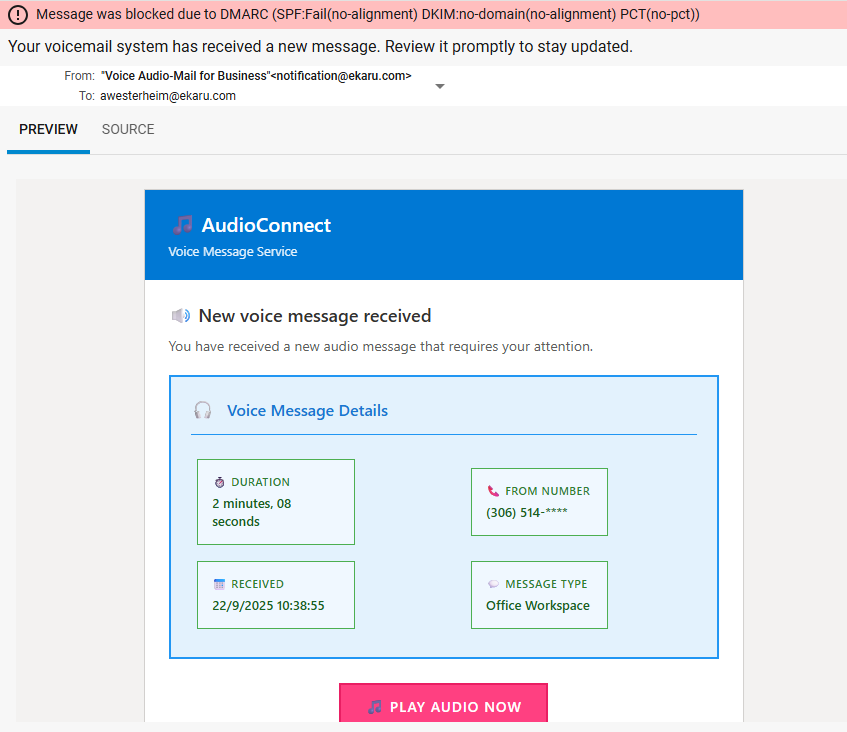
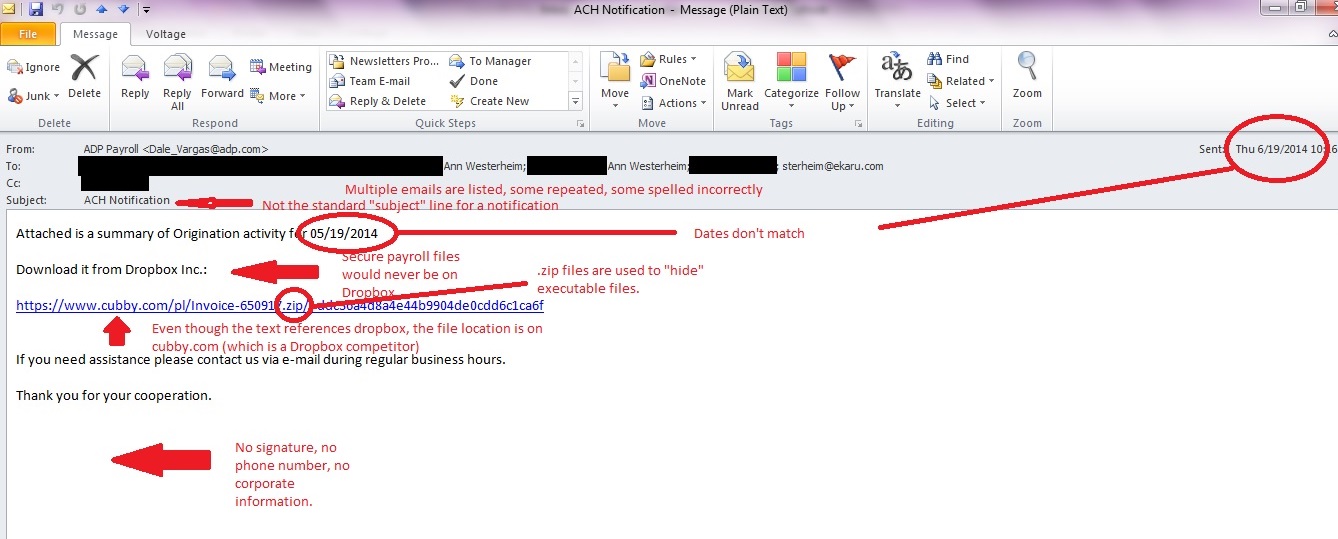
No system catches everything.
What happens if something does get through?
Read More.png)