Every year, Verizon publishes its Data Breach Investigations Report (DBIR), one of the most respected cybersecurity reports in the industry. The 2026 report analyzed more than 22,000 confirmed data breaches across 145 countries, making it one of the largest collections of real-world cybersecurity data available.
At Ekaru, we pay close attention to reports like this because they help us separate trends from headlines. Instead of relying on assumptions, we can see exactly how attackers are succeeding, where businesses are struggling, and what organizations can do to better protect themselves.
Before we dive into the findings, it's helpful to understand two terms you'll see throughout cybersecurity reports:
Incident: A security event that disrupts business operations, compromises systems, or creates a security risk.
Breach: A type of incident where sensitive information is actually accessed, stolen, or exposed to someone who shouldn't have it.
In other words, every breach is an incident, but not every incident becomes a breach. For example, a ransomware attack or website outage may be considered a security incident even if no customer or company data is stolen.
The biggest takeaway from this year's report is surprisingly simple:
Cybersecurity fundamentals matter more than ever.
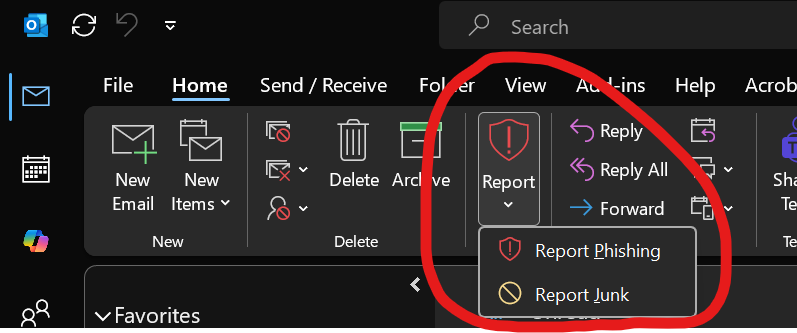
While artificial intelligence, ransomware, and sophisticated cybercriminal groups continue to dominate the news, most successful breaches still come down to a handful of preventable issues. Here are the lessons small businesses should take away from Verizon's findings.
Read More.png)