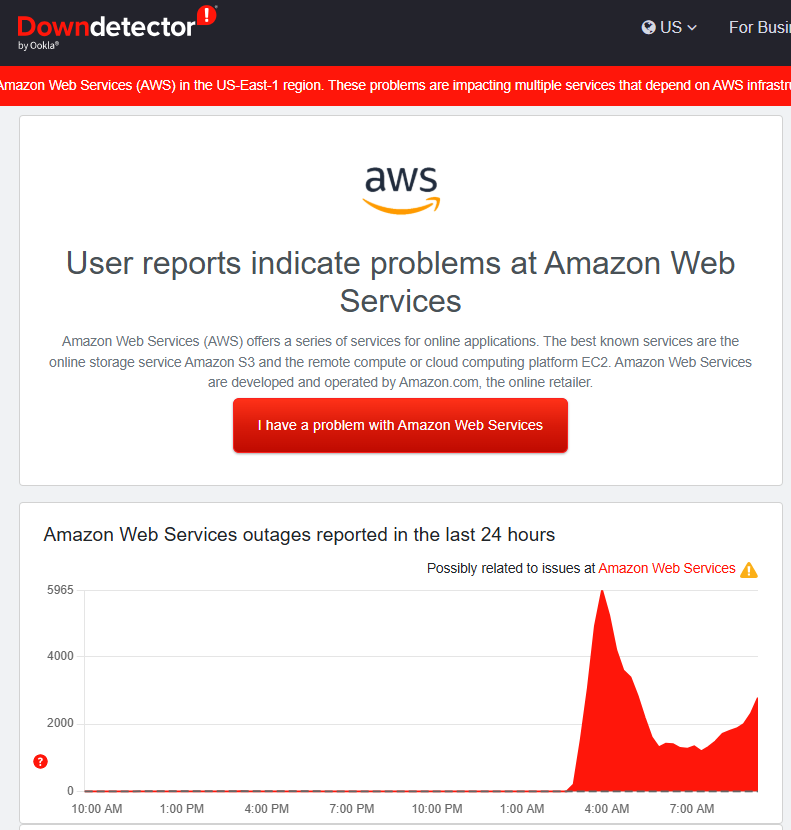
If your favorite app wouldn’t load this morning, you weren’t alone. Amazon Web Services (AWS) - the cloud backbone behind a huge slice of the internet - had a major hiccup in its US-EAST-1 (Northern Virginia) region in the early hours today. Reports began around ~3:00 a.m. ET, with recovery signs a couple hours later. By mid-morning, Amazon said the underlying issue had been fully mitigated. Still, the ripple effects were hard to miss: services like Snapchat, Zoom, Signal, Fortnite, Coinbase/Robinhood, Perplexity, and even airline sites such as Delta and United saw issues at points during the incident. DownDetector tallied millions of outage reports across the globe. The Verge
Read MoreTechnology Advisor Blog
It’s Raining in Boston - and in the Cloud: What Today’s AWS Outage Teaches Us
Posted by Ann Westerheim on 10/20/25 12:09 PM
Tags: small business, technology, cloud
What Really Happens When Your Email Gets Hacked (And How to Stop It)
Posted by Ann Westerheim on 10/17/25 4:08 PM
This week, we received what looked like an official Request for Proposal (RFP) email from a local business we know. It was well-written, professional, and completely believable.
Read MoreTags: eMail, cybersecurity, hack
Networks are The Powerhouse of a Business, They Must Be Protected
Posted by Sarah Carroll on 10/17/25 11:28 AM
When keeping business operations alive, security is essential. Security isn’t just strong passwords of 16 or more characters across multiple different websites/accounts, or MFA, it’s a deeper-rooted step to take with your networks to prevent most cybersecurity threats.
From a 2021 Verizon study, “61% of small to mid-size businesses experienced a cyberattack in 2021”. In 2023 73% of small businesses faced cyber-attacks. In 2024, 94% of small to medium sized businesses faced a cybersecurity attack. The number keeps increasing each year with small businesses affected. Something must be done to protect businesses from such cyber attacks.
The mindset has probably come up multiple times in conversation; “I’m a small business, I’m too small to be known for hackers to try and target me”. It’s not exactly if it happens, it all matters as to when. Don’t wait until that ‘when’ turns into ‘today’ when you receive a socially engineered scam that looks legit. Scams are becoming harder to identify, when you are not investing in proper cybersecurity measures, the wrong people will notice you do not have the tools or budget.
Tags: security protection, support, technology, network security, malware, security awareness training, online safety, Cybersecurity Awareness Training
MFA is Essential; Even if You Do Not Want Anything Work Related on Your Phone
Posted by Sarah Carroll on 10/10/25 10:21 AM
Are you someone that does not want any trace of work on your phone with the intent of separate work from home? Well, you’re not alone.
It’s understandable that you would want to have a personal device that has no affiliation to work or receive any work-related phone calls. However, with threat actors ruthlessly and creatively generating scams for folks to fall victim to, it’s important to understand the benefits of using multi factor authentication across multiple devices.
Tags: Phone System, Cybersecurity, email scams, Multi-Factor Authentication, MFA, Cybersecurity, Travel, Cybersecurity Awareness Training
Cold Weather Setting In, Cold Call Scams (Vishing) Are on The Rise
Posted by Sarah Carroll on 10/7/25 4:29 PM
October is here, and threat actors are ramping up their attacks to the point where its… spooky.
While Halloween is coming up, Thanksgiving and Christmas are also on the horizon, it’s more evident than ever we must remain hypervigilant and not fall for these intricate phishing attempts.
In September, many folks and including some of us in the office, experienced a rise in spam (Vishing) phone calls. You may be wondering ‘Where are all these unknown numbers coming from?” If you’re like me, when you notice an unknown caller ID notify your phone, you never pick up. However, not everyone is like that. However, the Ekaru team is here to teach you all about cold calling scams, how to identify them, reasons why they are potentially occurring, and the steps/services we provide to help protect yourself and others from falling into their trap.
Read MoreTags: small business, security protection, small business technology, small business technology advice., Phone System, cybersecurity, ransomware, cybersecurity, security awareness training, cybersecurity training, Cybersecurity Awareness Training
Choosing the Right MSP For Your Businesses Needs-Why Ekaru Is a Great Fit
Posted by Sarah Carroll on 10/3/25 12:14 PM
When businesses become further established and credible within their community, the conversations of increasing security measures, budgeting, and overall work morale begin to initiate for further discussion. Understandably, maintaining a growing business can be challenging and shifting your priorities, sometimes causing the complacent “My business won’t get hacked, I’m safe it won’t happen to me.” This type of thinking can backfire especially if you’re not paying close enough attention - there is no "Security by Obscurity"! At the end of the day, we have all been there and sometimes had to pay for the consequences.
Since there are so many aspects to a business that can pull you in several directions at once it’s hard to pinpoint where to begin conversations on cybersecurity needs. That’s where Ekaru comes in to provide you with the best IT solutions in the Boston Massachusetts area. To make informed decisions about your cybersecurity needs aligned within your budget.
Tags: small business, responsiveness, Monitoring, support, small business technology advice., cybersecurity, online safety, Cybersecurity, Social Media, Cybersecurity Awareness Training
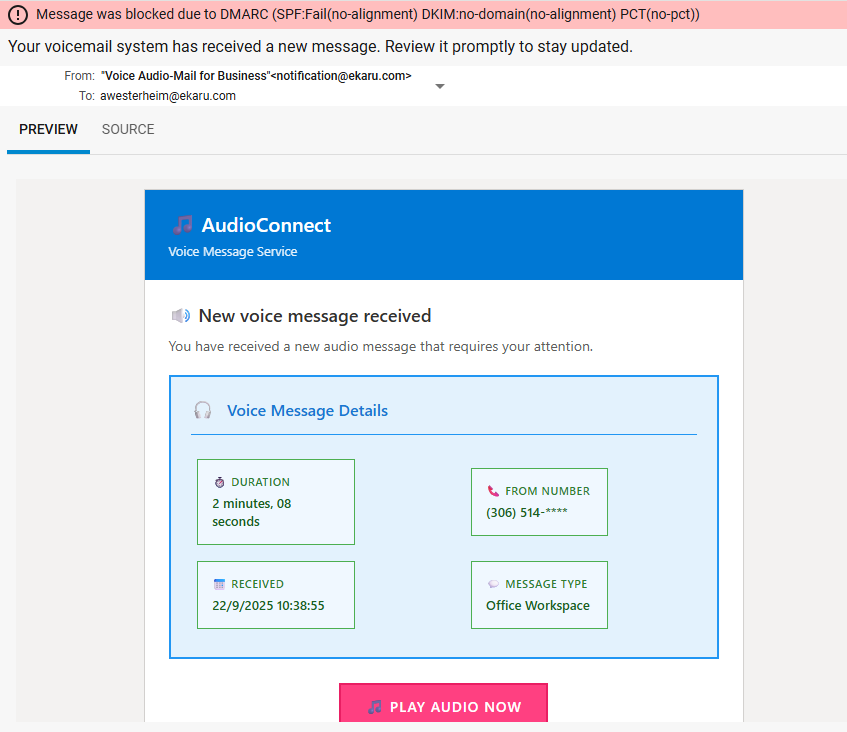
Why DMARC Matters: A Real-Life Voicemail Scam Example Every Business Should See
Posted by Ann Westerheim on 9/22/25 12:44 PM
Last week, I didn’t even see a suspicious voicemail notification in my inbox - and that’s the point! Our email security blocked it before it ever got to me. At first glance, the message looked pretty legitimate. It was well-formatted, had a sense of urgency - “Your voicemail system has received a new message. Review it promptly to stay updated”, and looked like something that could easily trick someone into clicking.
Read MoreTags: eMail, cybersecurity, DMARC, Cybersecurity Awareness Training
Got Electronics? Join Us For Ekaru's Quarterly Electronics Recycling Event!
Posted by Sarah Carroll on 9/18/25 4:45 PM
Aside from Ekaru’s qualified team providing IT solutions and cybersecurity awareness training, we enjoy giving back to our community.
When you purchase a new device such as a laptop, monitor, or a new smartphone, the first step is transferring all your essential data to the new device. Once you’ve transferred all the essentials, you’re left with your former device, inactive and collecting dust on the shelf.
Understanding the materials that create these tools we use in our everyday lives, it’s evident that you cannot just discard these devices in normal everyday trash bins.
Does this resonate that you recently got that new iPhone, MacBook or monitors? That’s where we come in! Our team at Ekaru hosts quarterly electronics recycling events supported by eWaste.
Read MoreTags: computer security, computer, technology, Security Requirements, productivity, small business technology advice., cybersecurity, data security, cybersecurity training, electronics recycling, Cybersecurity, Social Media
Goodbye Windows 10, Hello Windows 11: What Local Businesses Need to Know Before October 14, 2025
Posted by Ann Westerheim on 9/12/25 12:51 PM
Microsoft has officially announced that Windows 10 support will end on October 14, 2025. After that date, no more free security updates will be released. For small businesses, this isn’t just a technical detail - it’s a security and business risk. Cybercriminals often target outdated systems, and without regular patches, Windows 10 devices will quickly become vulnerable.
Read MoreTags: Microsoft, cybersecurity, windows 10
Ekaru Achieves Generative AI Certification from Breach Secure Now to Lead Clients in Secure, Strategic AI Adoption
Posted by Ann Westerheim on 9/3/25 6:18 PM
Ekaru, a trusted provider of managed IT and cybersecurity services, is proud to announce that we are now Generative AI Certified by Breach Secure Now (BSN). BSN is a leading provider of human-centric cybersecurity, AI awareness, and productivity training. This industry-first certification empowers our team to confidently lead clients through the complexities of AI adoption - safely, strategically, and securely.
Read MoreTags: small business technology, cybersecurity, AI
.png)