April 2026 Updates Released Today
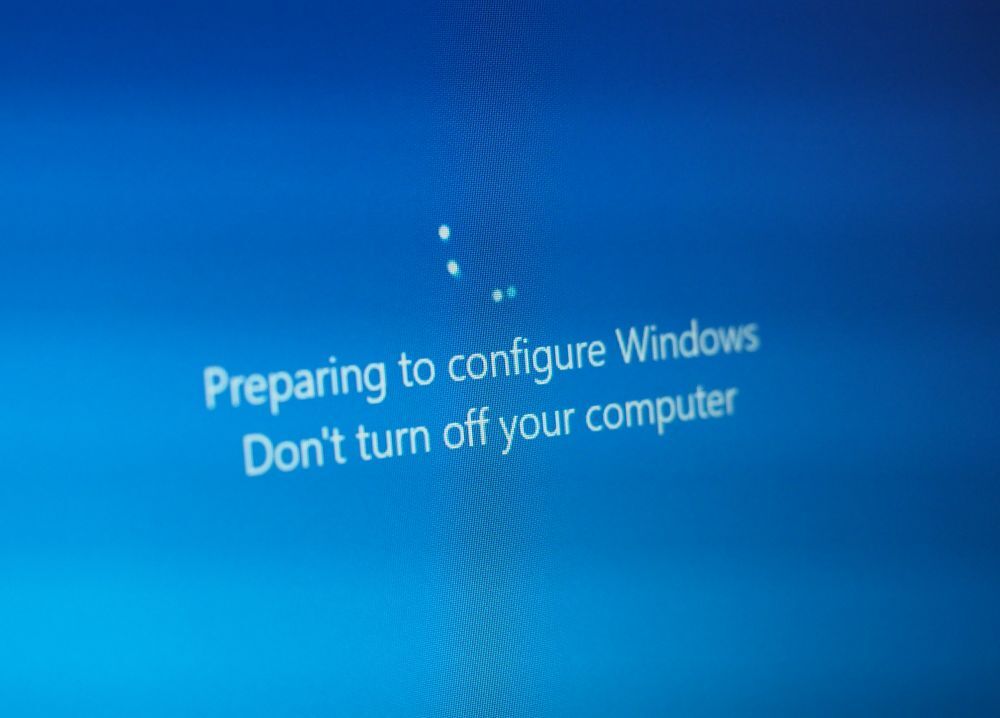
If your computer prompts you to restart today, you might be tempted to click Remind Me Later and move on with your day.
You wouldn’t be alone.
But that small pop-up is tied to one of the most important cybersecurity habits a business can have: staying current with updates.
Today is Patch Tuesday - the second Tuesday of each month, when Microsoft releases security updates, bug fixes, and system improvements for Windows and other Microsoft products. It happens quietly in the background for most people, but for IT teams and cybersecurity professionals, it’s a date we watch closely every single month. Microsoft publishes these releases through its official Security Update Guide each month.
At Ekaru, we pay attention to Patch Tuesday because these updates often fix the kinds of weaknesses attackers look for first. And while updates may seem routine, falling behind can create real risk.
Read More.png)