What It's Like to Work With Ekaru
Read MoreTechnology Advisor Blog
Tags: small business, Managed Services, managed IT services in Boston, IT services Boston, managed service provider Boston, Boston Ransomware
What the FBI’s Latest Cybercrime Report Means for Small Businesses
Posted by Ann Westerheim on 5/18/26 2:20 PM
When many people picture cybercrime, they imagine hackers breaking into giant corporations with sophisticated tools and complex code. But for most small businesses, cybercrime today looks much more ordinary - and much more personal.
-
It looks like an email from a trusted vendor asking for updated payment information.
-
It looks like a voicemail that sounds like a company executive requesting an urgent wire transfer.
-
It looks like a Microsoft 365 login page that appears completely legitimate.
And increasingly, thanks to artificial intelligence, these scams are becoming harder and harder to spot.
The FBI recently released its latest Internet Crime Complaint Center (IC3) report, highlighting billions of dollars in losses tied to cybercrime, including growing losses from AI-assisted scams and cryptocurrency fraud. While the numbers themselves are staggering, the bigger takeaway for local businesses is this:
Cybercriminals are getting better at pretending to be someone you trust.
Read MoreTags: cybersecurity, Cybersecurity Awareness Training, Cyber Crime
Windows 11 May 2026 Patch Tuesday: What Small Businesses Need to Know
Posted by Linda Hanson on 5/13/26 12:11 PM
Microsoft released its May 2026 Patch Tuesday security yesterday. Update KB5089549 is now rolling out to all Windows 11 devices. While this update isn't the flashiest release of the year, it includes improvements that small business owners and their teams will actually notice day to day, along with a critical security deadline that cannot be ignored.
Read MoreTags: Security, Patches, Microsoft, Microsoft Updates, Microsoft Security Patches, Patch Policy, Computer Tip, Security Awareness, Microsoft Windows 11 Update, New Features
What If They’re Already In? The Blind Spot in Email Security Most Businesses Miss
Posted by Ann Westerheim on 5/6/26 10:20 AM
We hear this all the time:
“We already have email security in place - we’re good.”
“We’re on Microsoft 365 (or Google Workspace) - they take care of that.”
And it’s easy to see why at first that feels like enough.
Platforms like Microsoft and Google provide a powerful foundation - offering the infrastructure, built-in protections, and security features that businesses rely on every day.
But here’s the part that often gets misunderstood:
They provide powerful tools - but they don’t replace a complete security strategy.
And even with strong protections in place…
No system catches everything.
What happens if something does get through?
Read MoreTags: eMail, cybersecurity, Microsoft 365
Ekaru Awarded GTIA Cybersecurity Trustmark for Excellence in Cybersecurity Practices
Posted by Ann Westerheim on 4/22/26 10:43 AM
Ekaru earned the GTIA Cybersecurity Trustmark, recognizing its commitment to secure, compliant IT practices and trusted client protection.
Ekaru, a leading provider of IT support, cybersecurity protection, cloud services, proudly announces its achievement of the Cybersecurity Trustmark issued by the Global Technology Industry Association (GTIA). The Trustmark confirms that Ekaru has undergone a rigorous review of its cybersecurity policies, procedures, and controls.
“Achieving the GTIA Cybersecurity Trustmark reinforces our promise to our clients: security isn’t a feature - it is our foundation,” said Dan Wensley, CEO of GTIA. “This recognition assures our partners and clients that their data is in trusted hands.”
The GTIA Cybersecurity Trustmark follows a detailed evaluation aligned with frameworks such as NIST and CISA. In addition, CREST-accredited third-party assessors ensure audit integrity to the Trustmark standard.
Read MoreTags: Compliance, cybersecurity
Today is Patch Tuesday: Why It Matters for Your Business
Posted by Ann Westerheim on 4/14/26 10:55 AM
April 2026 Updates Released Today
If your computer prompts you to restart today, you might be tempted to click Remind Me Later and move on with your day.
You wouldn’t be alone.
But that small pop-up is tied to one of the most important cybersecurity habits a business can have: staying current with updates.
Today is Patch Tuesday - the second Tuesday of each month, when Microsoft releases security updates, bug fixes, and system improvements for Windows and other Microsoft products. It happens quietly in the background for most people, but for IT teams and cybersecurity professionals, it’s a date we watch closely every single month. Microsoft publishes these releases through its official Security Update Guide each month.
At Ekaru, we pay attention to Patch Tuesday because these updates often fix the kinds of weaknesses attackers look for first. And while updates may seem routine, falling behind can create real risk.
Read MoreTags: Microsoft Updates, Microsoft Security Patches, cybersecurity
Color Coordinating Your Microsoft Outlook Inbox For Boosted Productivity
Posted by Sarah Carroll on 4/8/26 1:36 PM
Have you noticed your inbox becoming more cluttered? Are you using flagged messages to keep track of important messages and everything else gets lost in the noise of your active inbox? Well, you’re not alone, and there’s a rather colorful solution to assist with organizing your emails that transforms how you interact with your inbox! Emails are more than just keeping in contact with your colleagues and vendors, it’s a task manager, documentation hub, and what keeps your overall daily operations functioning. However, without a structured approach to organization, Outlook can quickly become overwhelming, leading to missed deadlines, overlooked messages, and increased stress.
Read MoreTags: Outlook, Microsoft Outlook, small business technology advice., cybersecurity, Tech Tips
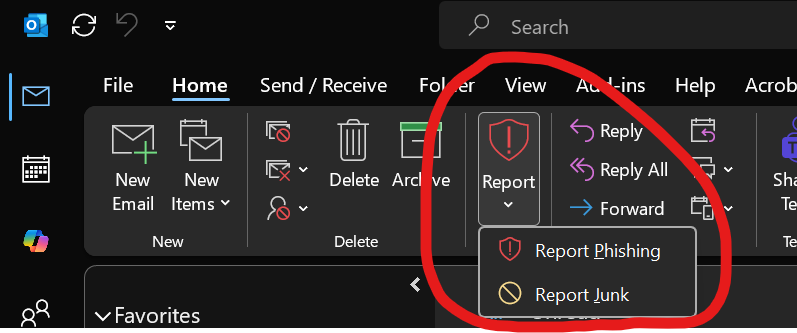
What Happens When You Click “Report Phishing” in Outlook? (And Why It Matters More Than You Think)
Posted by Ann Westerheim on 4/6/26 12:07 PM
📩 Most employees have seen it.
That little button in Outlook:
👉 “Report Phishing”
👉 “Report Junk”
During a recent Cybersecurity Town Hall with one of our clients in Boston, someone in the room asked about this button - The question most people haven't asked:
What actually happens when someone clicks it?
And more importantly - is anyone paying attention?
This is worth exploring.
Read MoreTags: Microsoft Outlook, cybersecurity, Cybersecurity Awareness Training
Last month, we discussed Windows 11 Updates that assisted individuals in increasing their overall security posture, productivity workflow, and expressive various widgets for user experience. As we are a quarter of the way through the year, a new and impactful wave of updates is approaching for those using Windows 11 systems.
Read MoreTags: Microsoft Windows Update, Microsoft, Managed Services, cybersecurity, Windows11, Windows 11, New Features
Not Sure If Your IT Support Is Good Enough? Here’s Where to Start
Posted by Ann Westerheim on 3/31/26 3:53 PM
We’ve had a few conversations recently with local business owners who all said some version of the same thing:
“I think our IT is fine… but I’m not really sure. Maybe we're not doing everything we should be doing.”
Nothing was obviously wrong. Systems were running. But underneath that was uncertainty - and when it comes to IT and cybersecurity, “I think we’re okay” isn’t the same as actually being protected.
Sometimes its the "One-man-show bottleneck":
Read More“We’ve been working with the same IT person for years, but I think we’ve outgrown them. It’s getting harder to reach them, and when something goes wrong, we’re kind of stuck waiting.”
Tags: small business, small business technology, cybersecurity, tech support
.png)