We’ve had a few conversations recently with local business owners who all said some version of the same thing:
“I think our IT is fine… but I’m not really sure. Maybe we're not doing everything we should be doing.”
Nothing was obviously wrong. Systems were running. But underneath that was uncertainty - and when it comes to IT and cybersecurity, “I think we’re okay” isn’t the same as actually being protected.
Sometimes its the "One-man-show bottleneck":
“We’ve been working with the same IT person for years, but I think we’ve outgrown them. It’s getting harder to reach them, and when something goes wrong, we’re kind of stuck waiting.”
Read More
Tags:
small business,
small business technology,
cybersecurity,
tech support

Amazon provides users with an extensive ecommerce platform, with purchases ranging from clothing, games, kitchen, niche topics, home décor, technology, and more right at your fingertips. Exceptional delivery time on everyday items, insightful reviews, and a great return policy. Though Amazon has millions of official and 3rd party sellers using its ecommerce platform in showcasing their products & services, there are risks to be aware of especially when buying laptops.
In recent months, we have heard reports of users buying computers from Amazon with complicated issues regarding unclear support policy plans and overall, not what they were expecting. In today’s blog post, we are going to discuss key risks that come with purchasing from 3rd party sellers on Amazon, with misleading specs and even receiving used items.
At Ekaru, our goal isn’t to instill fear but provide users with the most up-to-date cybersecurity findings to help you make informed decisions. Especially when it comes to your devices and overall cybersecurity hygiene. Located in Westford MA, we work alongside multiple small and medium-sized businesses in the Boston metropolitan area ranging from doctor offices, construction, attorney offices, accounting, and so much more.
Read More
Tags:
laptop,
small business,
RAM,
small business technology advice.,
specifications,
cybersecurity
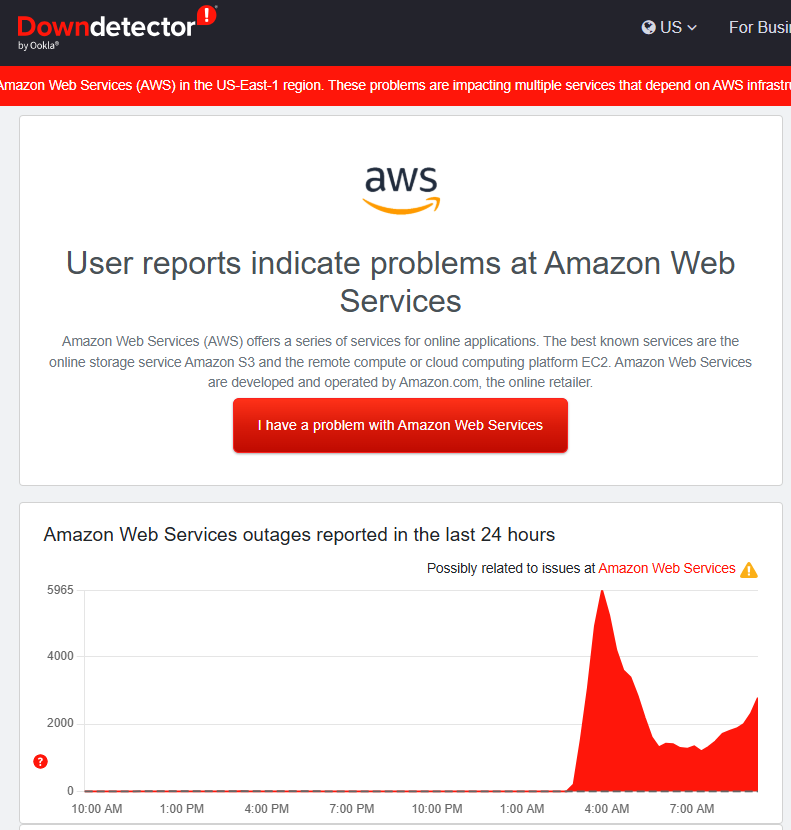
If your favorite app wouldn’t load this morning, you weren’t alone. Amazon Web Services (AWS) - the cloud backbone behind a huge slice of the internet - had a major hiccup in its US-EAST-1 (Northern Virginia) region in the early hours today. Reports began around ~3:00 a.m. ET, with recovery signs a couple hours later. By mid-morning, Amazon said the underlying issue had been fully mitigated. Still, the ripple effects were hard to miss: services like Snapchat, Zoom, Signal, Fortnite, Coinbase/Robinhood, Perplexity, and even airline sites such as Delta and United saw issues at points during the incident. DownDetector tallied millions of outage reports across the globe. The Verge
Read More
Tags:
small business,
technology,
cloud
October is here, and threat actors are ramping up their attacks to the point where its… spooky.
While Halloween is coming up, Thanksgiving and Christmas are also on the horizon, it’s more evident than ever we must remain hypervigilant and not fall for these intricate phishing attempts.
In September, many folks and including some of us in the office, experienced a rise in spam (Vishing) phone calls. You may be wondering ‘Where are all these unknown numbers coming from?” If you’re like me, when you notice an unknown caller ID notify your phone, you never pick up. However, not everyone is like that. However, the Ekaru team is here to teach you all about cold calling scams, how to identify them, reasons why they are potentially occurring, and the steps/services we provide to help protect yourself and others from falling into their trap.
Read More
Tags:
small business,
security protection,
small business technology,
small business technology advice.,
Phone System,
cybersecurity, ransomware,
cybersecurity,
security awareness training,
cybersecurity training,
Cybersecurity Awareness Training
When businesses become further established and credible within their community, the conversations of increasing security measures, budgeting, and overall work morale begin to initiate for further discussion. Understandably, maintaining a growing business can be challenging and shifting your priorities, sometimes causing the complacent “My business won’t get hacked, I’m safe it won’t happen to me.” This type of thinking can backfire especially if you’re not paying close enough attention - there is no "Security by Obscurity"! At the end of the day, we have all been there and sometimes had to pay for the consequences.
Since there are so many aspects to a business that can pull you in several directions at once it’s hard to pinpoint where to begin conversations on cybersecurity needs. That’s where Ekaru comes in to provide you with the best IT solutions in the Boston Massachusetts area. To make informed decisions about your cybersecurity needs aligned within your budget.
Read More
Tags:
small business,
responsiveness,
Monitoring,
support,
small business technology advice.,
cybersecurity,
online safety,
Cybersecurity, Social Media,
Cybersecurity Awareness Training
When it comes to establishing your business on a social media platform, a lot of teamwork and insight goes into its strategy. These calculations apply to tone, values, visuals, color, and messaging to find the right audience to interact with your content. What’s also important in maintaining social media is the security of general accounts and who monitors activity across these accounts. In the case of our social media presence at Ekaru, a small business MSP specializing in cybersecurity located within the outer metropolitan area of Boston serving small to medium sized clients. Our values are to be friendly, helpful, insightful, provide knowledgeable articles that align, bring up conversations surrounding awareness of good and bad cybersecurity practices to learn from. Along with cybersecurity practices to implement within your business, questions you may ask yourself are ‘how can I maintain a healthy social media presence that can apply for my business and self?
Read More
Tags:
small business,
passwords,
strong passwords,
security protection,
Monitoring,
small business technology advice.,
cybersecurity,
security awareness training,
cybersecurity training,
Cybersecurity, Social Media
Have you ever been hooked to a phishing attempt? Did you know that phishing is involved in 70% of breaches? Whether it’s an email, phone call, or text message, these are some of the common ways bad actors use to obtain your personal and financial information for malicious gain. Phishing emails were introduced into our lives decade(s) ago and have grown increasingly creative and sophisticated with native language use and perfect grammar.
Read More
Tags:
small business,
phishing,
Cybersecurity, email scams,
cybersecurity, ransomware,
data security,
spoofing,
Security Awareness,
email spoofing
Cybersecurity Insurance for small business offers protection that standard business coverage often overlooks. Your company faces mounting risks from data breaches, ransomware attacks, and operational disruptions due to cyber incidents - problems that traditional insurance policies were not built to handle.
Read More
Tags:
small business,
cybersecurity,
Cyber Insurance
Do small businesses need cybersecurity? YES! Data shows that half of all cyber attacks target small organizations, making them prime targets alongside large corporations. Major security breaches at Fortune 500 companies grab headlines, yet local businesses, nonprofits, and municipalities face ongoing threats that can expose donor databases, financial records, and private customer details. Each year, Verizon publishes the Data Breach Investigations Report which is loaded with statistics on the latest updates on real-world breaches. Reports like this make it clear: small businesses aren't flying under the radar - they're in the crosshairs. Understanding real-world breach data helps you prepare, protect and stay resilient.
Read More
Tags:
small business,
cybersecurity,
incident response
What to do after a cyber attack requires fast, strategic action to protect your business and stop further damage. A well-planned response can mean the difference between a brief disruption and a complete business shutdown that costs hundreds of thousands of dollars.
Your response in the first 24 hours shapes your recovery path and impacts your ability to resume operations. This guide outlines the proven recovery methods that have helped businesses survive attacks and rebuild stronger, plus practical steps to prevent future incidents from harming your operations. You'll learn exactly which actions to take, who to call, and how to minimize both financial losses and operational downtime.
Read More
Tags:
small business,
small business technology advice.,
cybersecurity,
incident response
.png)