 Business email compromise, or BEC, is not always about a suspicious email. Sometimes the real danger is an attacker quietly using a real account while your business has no idea.
Business email compromise, or BEC, is not always about a suspicious email. Sometimes the real danger is an attacker quietly using a real account while your business has no idea.
When most people think about email security, they picture a suspicious message landing in someone’s inbox. Maybe it has a strange link, awkward wording, or a request that feels just a little off.
That is still a very real problem. But some of the most damaging email-related attacks do not start with an obviously fake message. They start when a criminal gets access to a real Microsoft 365 account and begins quietly looking around.
That is what makes business email compromise so dangerous.
In many cases, there is no loud warning sign. No flashing red light. No obvious signal that someone is inside a mailbox, reading conversations, watching financial activity, or waiting for the right moment to step in.
And for many small and midsized businesses, the uncomfortable question is this:
If someone were accessing your Microsoft 365 right now, would you know?
Business Email Compromise Often Looks Normal
Business email compromise is one of the most effective threats facing small businesses because it often blends in with everyday work. Instead of sending a generic scam email to hundreds of people, an attacker may gain access to a real account and take their time. They may read messages, learn how your team communicates, and watch for the right opportunity involving payroll, invoices, payment changes, or a sensitive customer conversation.
Then, at exactly the wrong moment, they step in.
The message may come from a real account.
The tone may sound normal.
The request may fit the conversation.
That is why these attacks can be so hard to spot.
“But We Have MFA” Is Not the End of the Story
Multi-factor authentication is incredibly important. Every business should be using it. It adds a critical layer of protection and stops many common attacks.
But MFA is not the same thing as guaranteed protection.
If an employee clicks on a phishing email, an attacker may still be able to get in through techniques like token theft. In plain English, that can mean the attacker captures the proof that the user already successfully signed in, allowing them to act like that user without having to go through the login process the normal way.
We've seen examples recently of people clicking on a link for a shared file, and then being prompted to log into Microsoft 365, sometimes by scanning a QR Code. This can look like an extra layer of security, but its actually a trick to steal your credentials. This is one reason Security Awareness Training matters so much - The extra login could appear like enhanced security to an untrained person, or could just slip by for a person who's very busy. Employees need help recognizing phishing attempts before they click, because even strong protections can be undermined when someone is tricked at the wrong moment.
MFA matters. Security Awareness Training matters. But neither one means a business would automatically know if an account has been compromised.
The Real Problem for Many SMBs: No Visibility
A lot of small businesses have tools designed to block bad email. That is important, but it is only one part of the picture.
What is often missing is visibility into what happens if a real account is compromised, and automated actions to freeze the account.
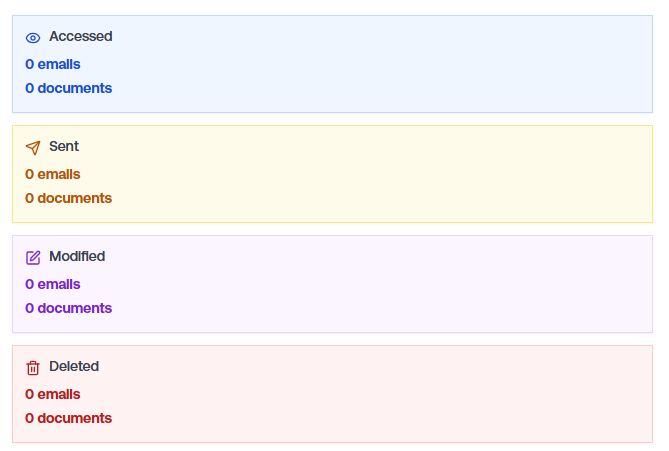
Could you tell if:
- someone logged into Microsoft 365 from an unusual location?
- a mailbox rule was created to quietly hide certain messages?
- someone was reading email behind the scenes before taking action?
- a user account started behaving in a way that did not match normal activity?
Without the right detection in place, many businesses are essentially flying blind.
And that is where business email compromise becomes especially dangerous. It can look completely ordinary until the damage is already done.
We’ve Seen the Difference Firsthand
In the past few months, we have seen several business email compromise cases where the signs of compromise could be analyzed quickly using the right tools. In those situations, it was possible to understand what was happening and stop it almost immediately, which can make a huge difference in the outcome.
Even with strong email protection and regular Security Awareness Training, people are still people. All it takes is the right message at the wrong moment.
Recently, we worked with a business where a user interacted with a phishing email. This is exactly the kind of situation that makes many organizations nervous, because the immediate question is: Did anything happen behind the scenes?
In this case, we were able to analyze the activity right away using tools designed to detect suspicious account behavior inside Microsoft 365.
The result was reassuring.
There was no evidence of unauthorized access.
No unusual logins.
No mailbox rules created.
No signs that the account had been used in a way it shouldn’t have been.
Just as importantly, we had clear visibility to confirm that.
When someone clicks, the real question is: what happened next - and can you prove it?
How's that for peace of mind?
We have also seen the other side of it.
When that visibility is not in place, it becomes much harder to answer the questions that matter most. Is someone in the account right now? What did they access? How long have they been there? What changed? Who else may be affected?
That uncertainty is a big problem, especially when time matters.
Why This Hits Small Businesses Hard
Sometimes small business owners assume they are not likely targets, or that attacks like this mainly affect larger organizations. Unfortunately, that is not how attackers think. Criminals can send out a million emails at no cost, and all they need are a few clicks to earn a payday.
Small and midsized businesses are often appealing because they move quickly, rely heavily on email, and may not have the same level of monitoring in place as a larger company. If an attacker can get into a real account and stay unnoticed, that can be enough.
And the consequences are not limited to financial fraud. A compromised Microsoft 365 account can affect customer trust, internal operations, vendor relationships, and your team’s confidence in what is real.
Good Security Is Not Just About Prevention
We all want to stop attacks before they happen. Of course we do.
But good security also means being able to detect suspicious activity quickly and respond before a bad situation gets worse.
That includes:
- strong phishing protection
- multi-factor authentication
- Security Awareness Training
- careful account and access management
- visibility into suspicious account and identity activity inside Microsoft 365
Because if someone does get through, the question becomes how quickly you can tell.
And that can be the difference between a close call and a much bigger problem.
A Better Question to Ask
If your business relies on Microsoft 365 every day, it is worth asking:
Would we know if one of our accounts had been compromised?
Not eventually.
Not after a customer notices something odd.
Not after money is sent to the wrong place.
Not after someone says, “I never sent that.”
Would you know soon enough to do something about it?
That is a much more important question than many businesses realize.
Smart, Practical Steps Can Make a Big Difference
Business email compromise is not just about suspicious emails anymore. Sometimes the bigger risk is that an attacker is using a real account in a way that looks perfectly normal from the outside.
That is why prevention matters. It is why Security Awareness Training matters. And it is why visibility matters.
If you’re not sure whether your business could spot this kind of activity in Microsoft 365, it may be time for a closer look. Multi-factor authentication, Security Awareness Training, and strong email protection all play an important role - but visibility is just as critical. Monitoring for suspicious activity helps you catch what slips through and stop it before real damage is done.
If you would like a second set of eyes on your Microsoft 365 security, we’re always happy to have a practical, no-pressure conversation about what you have in place today and where there may be gaps. Contact us!
About the author:
Ann Westerheim, PhD is the Founder and President of Ekaru, a Technology Service Provider of cybersecurity and IT services for small and medium businesses in the greater Boston area. Ann is an accomplished technology innovator and leader with three engineering degrees from MIT. She has twenty years of high tech experience in research, advanced development, product development, and as an entrepreneur. Her career has spanned a vast range of technology endeavors including research in thin film semiconductors and superconductors, microprocessor fabrication, development of early Internet medical applications, and now focusing on the application of technology in business. She has an avid focus on the "last mile" of technology and decreasing the digital divide.
.png)
